Hey OpenEMR community,
I’ve been working on a fully automated deployment of OpenEMR on Red Hat OpenShift using the new ambient mode service mesh — and I wanted to share it with the community since healthcare IT folks ask about security and compliance posture pretty regularly here.
What it does:
-
Deploys OpenEMR + MariaDB + Redis on OpenShift with a single script or Ansible playbook
-
Enforces mTLS between all services automatically — no code changes, no sidecars, no certificate management
-
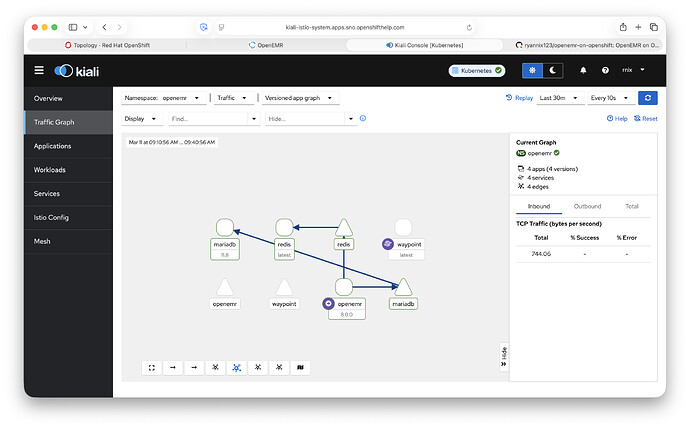
Zero-trust AuthorizationPolicies: OpenEMR can reach MariaDB and Redis, nothing else can, full stop
-
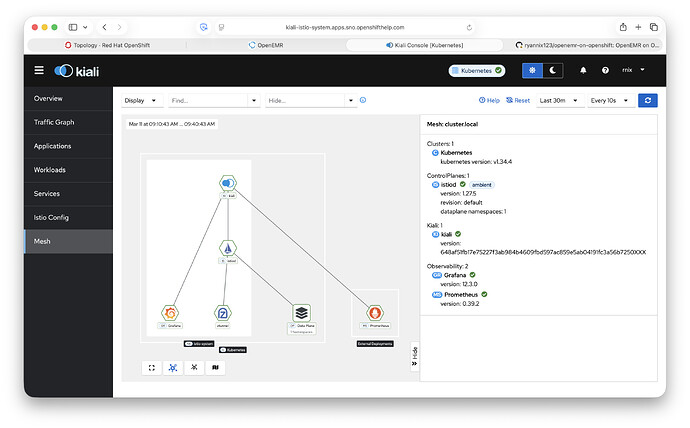
Kiali traffic graph gives you a live visual of every connection in the mesh with mTLS status
-
Let’s Encrypt wildcard TLS on the ingress
-
Runs under OpenShift’s restricted SCC — no privileged containers
Why it matters for healthcare:
HIPAA requires encryption in transit and access controls between system components. This architecture gives you both enforced at the infrastructure layer — meaning it holds even if OpenEMR itself is misconfigured. It’s also fully auditable through Kiali and Grafana dashboards.
It’s a sub-folder on my repo: https://github.com/ryannix123/openemr-on-openshift/tree/main/service-mesh
Fair warning: ambient mode on OpenShift is bleeding edge and took some serious digging to get working. The README includes a full troubleshooting guide for every failure mode I’ve encountered. Happy to answer questions here or in the repo issues. Also, this deployment can’t be used on the free OpenShift Developer Sandbox just yet because ServiceMesh 3 isn’t installed. You’ll need your own OpenShift environment, which you can deploy on a single node.